This guide, [openvpn.net] has a good guide to setting up an OpenVPN server on a Linux machine. I used this guide as the other guides online are not as good and often do not lead to a satisfactory result.
I am using one on Linux and I can connect to it on my Windows machine and get an IP of 10.8.0.6.
Ensure this option is set to 1 to ensure that packet forwarding is enabled on the system. This would be desired for our VPN connection.
# Disables packet forwarding net.ipv4.ip_forward = 1 |
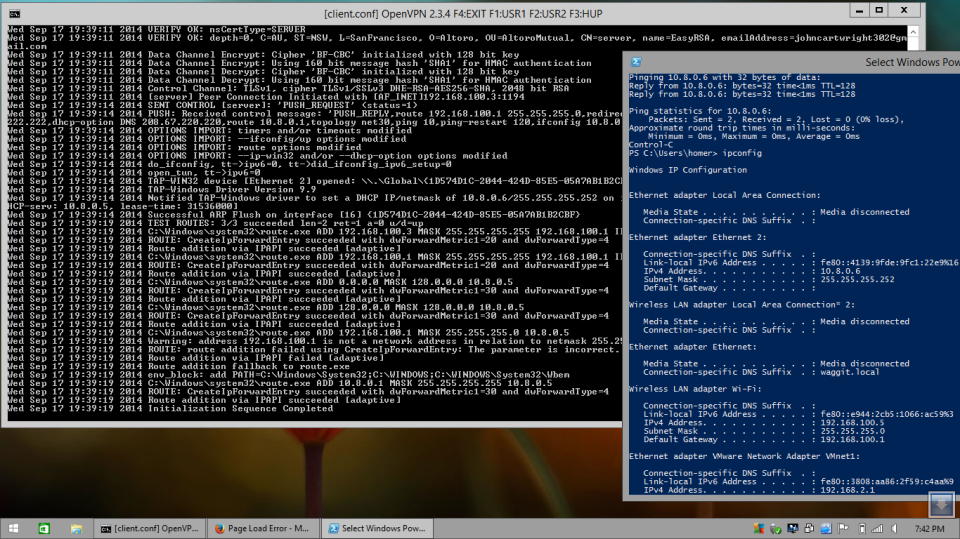
Copy all of your keys onto your Windows machine into a new folder and then run CMD as an Administrator. Then type openvpn client.conf
to attempt to run the client configuration and connect to your VPN. If you are successful, you will see the output in the screenshot above. Type ipconfig to check that you are getting a proper IP address. This is easy when you are following a proper tutorial and the keys are properly generated. The best way to create a Virtual Private Network is to use the 2048 bit encryption instead of 1024. This will greatly increase security exponentially. And do not use a PPTP VPN, this is not as secure.
To create VPN keys quickly, use this command.
sudo apt-get install easy-rsa openvpn |
Then copy the /usr/share/doc/openvpn/examples/easy-rsa directory to your home directory. This contains the scripts necessary to create a useful VPN configuration.
To ensure the consistent use of values when generating the Public Key Infrastructure, set the default values to be used by the PKI generating scripts. Edit ~/easy-rsa/vars and set these values at a minimum.
- KEY_COUNTRY
- KEY_PROVINCE
- KEY_CITY
- KEY_ORG
- KEY_EMAIL
Another thing to check is that you are using 2048 bit encryption. Set this option in vars as well.
# Increase this to 2048 if you # are paranoid. This will slow # down TLS negotiation performance # as well as the one-time DH parms # generation process. export KEY_SIZE=2048 |
Once this is complete, load the values.
source ./vars |
And then remove any previously generated certificates.
./clean-all |
Then generate the Certificate Authority (CA) certificate with this command.
./build-ca |
Build a server key with this command. Where foobar is your server hostname. Do not enter a challenge password or company name when the script prompts you for one. This will cause much heartache later.
./build-key-server foobar |
Now generate the Diffie-Hellman parameters .pem file needed by the server.
./build-dh |
Now build a key for the client computer to use when connecting to your OpenVPN server.
./build-key mycomputer1 |
Now you can copy these keys to the client computer and test the connection. There is some information about routed lans on this page: https://community.openvpn.net/openvpn/wiki/RoutedLans. This will help when setting up routing for your VPN.
Rosehosting also offer a simple OpenVPN installation script for creating a new OpenVPN instance on Ubuntu and getting a new user created.
View it here: https://www.rosehosting.com/blog/openvpn-setup-script-for-debian-and-ubuntu/.
Hi,
I found setting up openvpn to be a pain in the as* for me. Everytime I try to set it up manually, something is not working right. Luckily, I used this automated openvpn installer script which worked perfectly fine on my ubuntu ssd powered vps.
Now I can use my US vpn from Sydney without a problem. thanks to you, I understand now that generating another openvpn certificate is as easy as running ‘./build-key another-pc’.
Thank you